7 Lessons From The Intune Pros
Since Intune manages the entire lifecycle of such a broad array of hardware, it’s easy to assume it can do everything for every device. eGroup | Enabling Technologies’ field engineers deal with real-world challenges every day that push the boundaries. Recently, experts from eGroup | Enabling Technologies’ Intune practice discussed common issues and how to overcome them. Among other things, they shared lessons about policy assignment, Apple certificate expiration, hybrid Entra ID join, and Autopilot zero-touch deployment. Read or watch (below) their commentary for some key takeaways—there’s something for every stage of maturity.
Lesson 1: Planning for Policy Assignment
One of the major decisions to make in the planning phase is about how to assign device or application policies. A policy is a set of security and configuration settings that you then assign to a user or device.
Usually, organizations set up policies for company-owned devices (Windows, MacOS), such as BYOD Android, BYOD iOS, and sometimes company-owned Android or iOS.
In fact, the following kinds of policies can be created and assigned to users or groups.
Decide early on whether to assign policies by user or by group. Intune does not play well when you mix or match, and there may be conflicts. Conflicts can happen when different policies are applied to the same device but with different settings. For example, two policies may have different settings for the app copy/paste setting. Decide on standard configurations to minimize conflicting settings.
Lesson 2: Setting Expectations About Autopilot
Autopilot can enable zero-touch deployments in the right situation. If the user device will only be joined to Entra ID (fka Azure AD), then a zero-touch deployment is feasible. The OEM hardware provider (Dell, HP, Microsoft) can inject their hardware hashes into Intune automatically upon purchase, and then direct-ship the PC to a new person’s home office.
But if the device needs to hybrid join with the on-premises Active Directory, or if Group Policy (GPO) settings are applied, then line of sight (LAN/intranet) access to a Domain Controller is necessary.
Of course, it’s possible to mix and match based on the user and device needs. The key is getting the Autopilot profile setup right, assigning it to the right users or groups, and ensuring the app policies are configured correctly. Take a step back and evaluate if your end goal and your requirements can match.
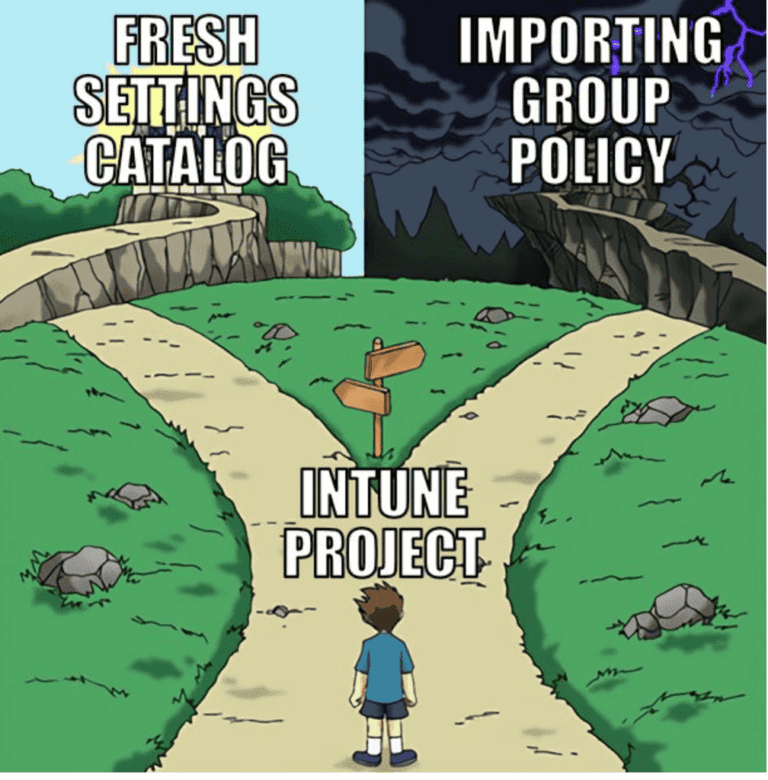
Lesson 3: Challenge Conventions
Intune doesn’t deliver all of the conventional settings of Active Directory GPOs, which were invented in Windows 2000. Microsoft continues to work on the GPO Analyzer to (in theory) translate old rules into new settings. However, it’s more prudent to challenge common assumptions and start with a clean slate.
Want to move much faster with Intune? Organizations who do think of, “How can we use Intune’s settings to adequately secure and manage these devices?” move much faster and more efficiently than those thinking, “How can we get all these GPOs into Intune?”.
Credit to Lewis Barry for this appropriate meme.
Lesson 4: Phish-Proof User Identities with Intune
While Intune is primarily focused on device management and security, it plays a role in preventing phishing attacks by enforcing device compliance policies. Here’s how:
Lesson 5: Expiring Certificates
Another common issue is that settings made in piloting or testing are overlooked or forgotten once in full production. An example is APNs certificate expiration or misconfiguration. Intune uses the Apple Push Notification service to communicate securely to your enrolled iOS devices, after a certificate is installed in Intune. An engineer originally piloting Intune or just dipping their toe in, may set APNs up with a personal account. If they overlook the expiration, and the certificate expires or was misconfigured, it’s necessary to reconfigure or contact Apple support to rectify the situation.
Set up notifications to be alerted when a certificate is about to expire. If it expires, devices won’t check in. While 30-day grace periods may be advertised, that’s been found to be shorter. Learn more about APNs troubleshooting below.
Lesson 6: Troubleshooting Tool
You can use the built-in troubleshooting feature to review different compliance and configuration statuses. For instance, entering in a user’s UPN will quickly show if they’re licensed or not, or if there are other issues. This is especially helpful if using the group-based licensing model.
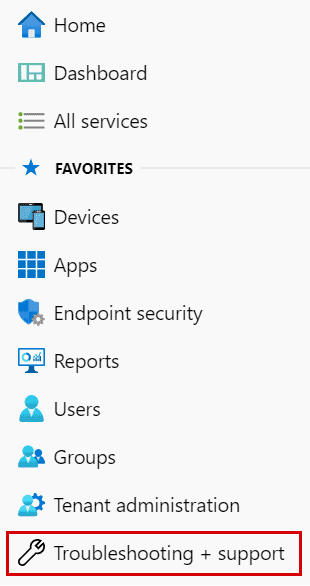
Other Intune troubleshooting resources are available.
Lesson 7: Patching Apps
Intune is excellent at managing and patching:
What about line of business (LOB) apps, or Win32 apps, that aren’t in the store? If the app requires supersedence (wiping then replacing or upgrading one version with another), only advanced Intune administrators will be successful. Such brave folks do the prework ahead of time to package the app, download the tools, and the steps involved with supersedence.
Off-the-shelf tools like Patch My PC are purpose-built for such apps, and Microsoft has mentioned an upcoming capability within the Intune Suite add-on SKU to manage such apps. Another interesting feature of the Intune Suite is Endpoint Privileged Management, which allows users to run as a standard user (without administrator rights), but still complete tasks that require elevated privileges.
Full Details can be found in the video below. If you have any suggestions for what our experts should cover next time, give us a shout!
New Capabilities from Intune Just Released!
Mobile App Management for Windows is now generally available. You can now enable protected MAM access to organization data via Microsoft Edge on personal Windows devices. Intune Mobile Application Management (MAM) for Windows is available for Windows 11, build 10.0.22621 (22H2) or later.
Intune integration with the Zebra Lifeguard Over-the-Air service is generally available, to allow delivery of OS updates and security patches over-the-air to eligible Zebra devices that are enrolled with Intune. You can select the firmware version you want to deploy, set a schedule, and stagger update downloads and installs. This integration is now generally available for Android Enterprise Dedicated and Fully Managed Zebra devices that are running Android 8 or later, and requires an account with Zebra, as well as Intune Plan 2, or Microsoft Intune Suite.
The Remote Help web app now allows users to connect to macOS devices and join a view-only remote assistance session. Intune Suite or Remote Help licensing is required.
Since Apple released iOS/iPadOS version 17, the minimum version now supported by Intune is iOS/iPadOS 15.x.
Group Policy analytics is generally available (GA). Use Group Policy analytics to analyze your on-premises group policy objects (GPOs) for their migration to Intune policy settings.

CTO & VP if Strategy - eGroup | Enabling Technologies
Contact our team of experts to discuss the specific needs of your organization!